TheHive Project French Chefs are very happy to announce Mellifera 13 (TheHive 2.13.0), a brand new, all shiny, major version of TheHive.
This new edition of your favorite Security Incident Response Platform (SIRP) has been cooked with great care to bring you a number of key features.
Mellifera 13 now uses ElasticSearch 5.x. We have tested it with v 5.5 but it should work just fine with ES 5.6.
Webhooks
TheHive has now basic support for webhooks. This allows your SIRP to post all the audit trail data to one or multiple webhooks defined in the configuration file. This way, you can listen to any change taking place on the platform and act on it as you see fit: create a ticket in an IT ticketing system, send a message to a Slack channel, display selected events of the audit trail on a screen, wake up your fellow analysts from sleep when a specific type of cases or a given alert is raised & so on. So get some elbow grease and code that Slack bot promptly 😉
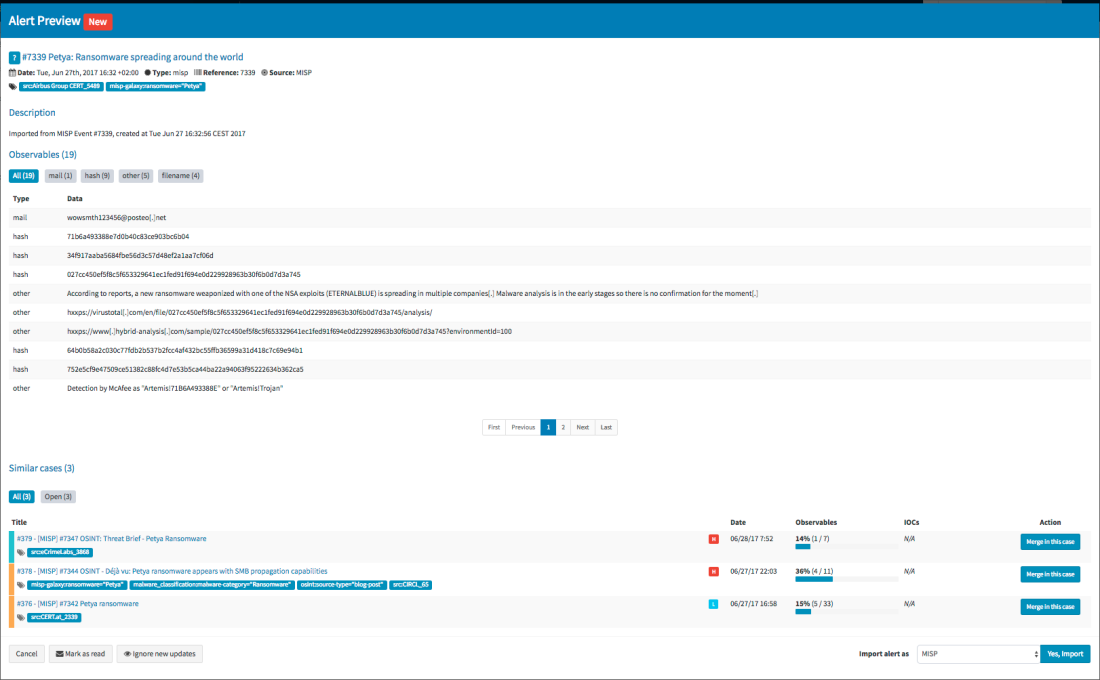
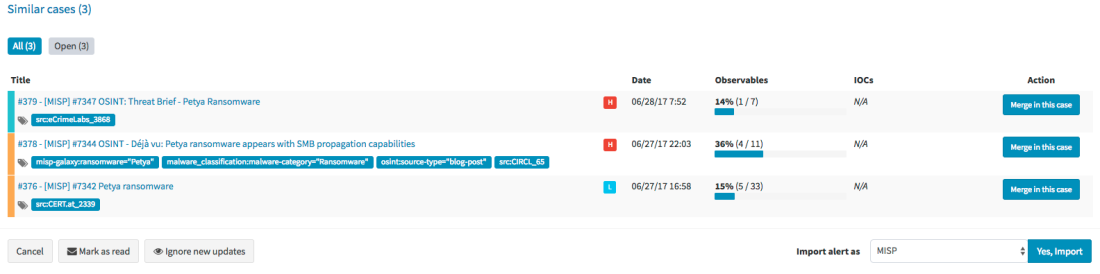
Import and Export from Multiple MISP Servers
Mellifera 13 can not only import events from multiple MISP servers but also export cases as events to one or several MISP instances. The exported cases will not be published automatically though as they need to be reviewed prior to publishing.



We strongly advise you to review the categories and types of attributes at least, before publishing the corresponding MISP events. Please also note that only and all the observables marked as IOCs will be used to create the MISP event. Any other observable will not be shared. This is not configurable. For further details, check the documentation.


API Keys
Mellifera 13 introduce a new authentication mechanism: API keys. This auth method is recommended for all programs or scripts, including your SIEM, that raise alerts on TheHive. You can, as an administrator, generate and revoke as many API keys as you want. Existing software using the basic authentication method should be modified to use API keys. But do not panic, while the basic authentication mechanism has been disabled by default, you can still enable it in application.conf.
The ‘alert’ role
A new alert role has been added. Only users with this role can create an alert. All existing programs which create alerts must have this role. Otherwise they will no longer work.
Download & Get Down to Work
If you have an existing installation of TheHive, please follow the migration guide. This is paramount to ensure a good transition from earlier versions. You have been warned.
If you are performing a fresh installation, read the installation guide corresponding to your needs and enjoy. Please note that you can install TheHive using an RPM or DEB package, use Docker, install it from a binary or build it from sources.
Support
Something does not work as expected? You have troubles installing or upgrading? No worries, please join our user forum, contact us on Gitter, or send us an email at support@thehive-project.org. We are here to help.