Didn’t you think we were going to holidays without letting few new stuff to play with ? 6 new Analyzers and 1 Responder complete the growing list of Neurons.
A Huge thanks to all the contributors for the great new features, without forgetting the work regarding improvements and bug fixes.
Documentation
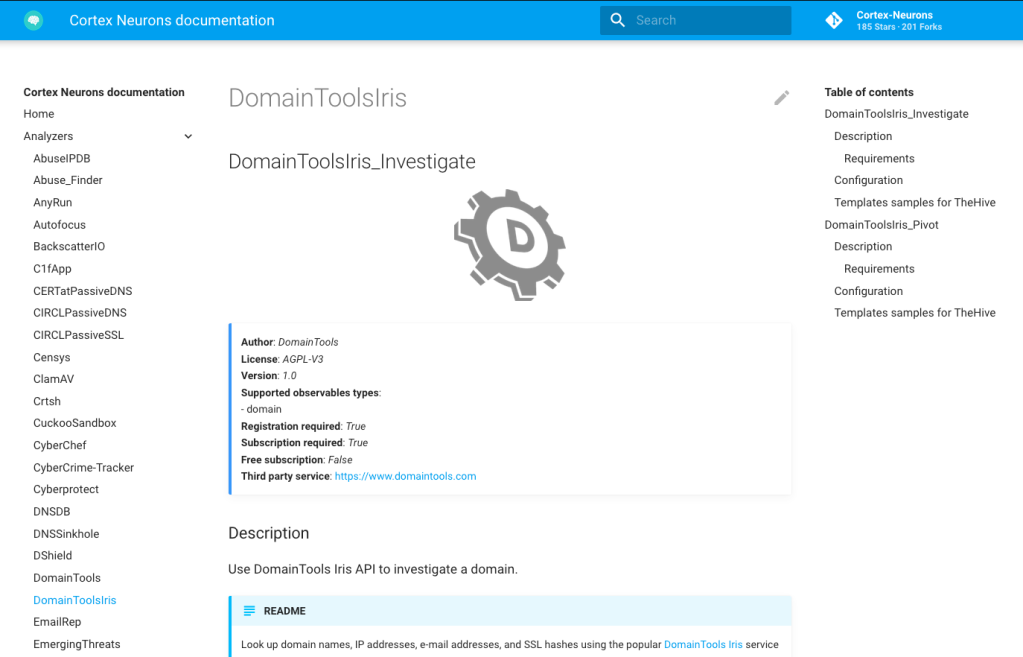
Find the complete documentation of Analyzers and Responders at the dedicated website: https://thehive-project.github.io/Cortex-Analyzers/
For each Analyzer and Responder, a page details the purpose of each flavor, the configuration required and even some screenshots from report samples.
New Analyzers
- DomainMailSPFDMARC contributed by @torsolaso and & Davide Arcuri (@dadokkio) ( #507 and #813)
- ForcepointWebsensePing contributed by Andrea Garavaglia (@garanews) & Davide Arcuri (@dadokkio) from LDO-CERT (#836)
- NERD contributed by Václav Bartoš (@vaclavbartos) from CESNET (#816)
- SekoiaIntelligenceCenter contributed by SEKOIA (#780)
- Spamassassin contributed by Andrea Garavaglia (@garanews) & Davide Arcuri (@dadokkio) from LDO-CERT (#811)
- Splunk contributed by @Unit777, @LetMeR00t (#534)
New Responder
- Velociraptor contributed by Wes Lambert (#803)
Fixes and Improvements
- Fix a bug in Hashdd_Detail_1_0 analyzer (#831)
- Fix a bug in PhishingInitiative_Scan_1_0 analyzer (#832)
- Fix a bug related to dataType in MalwareBazaar_1_0 analyzer (#830)
- Fix a bug in MISPWarninglists analyzer (#827)
- Fix a bug in Mailer_1_0 responder (#835)
Analyzers
DomainMailSPFDMARC
This analyzer comes in 1 flavor and let you check SPF (Sender Policy Framework) and DMARC (Domain-based Message Authentication, Reporting and Conformance) status of a domain or fqdn.
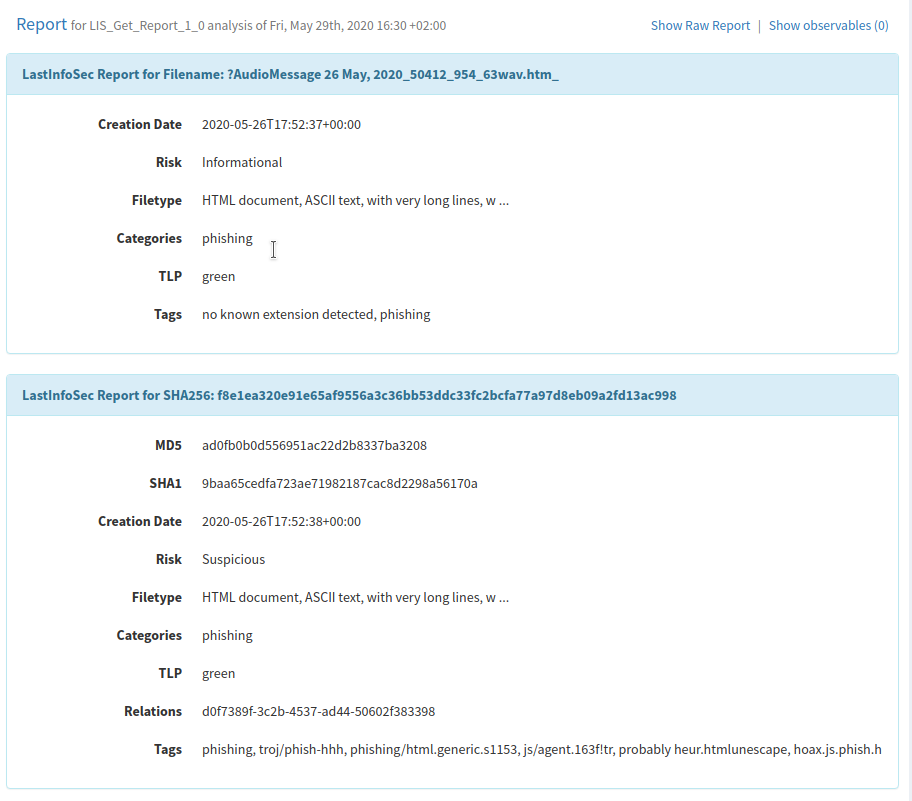
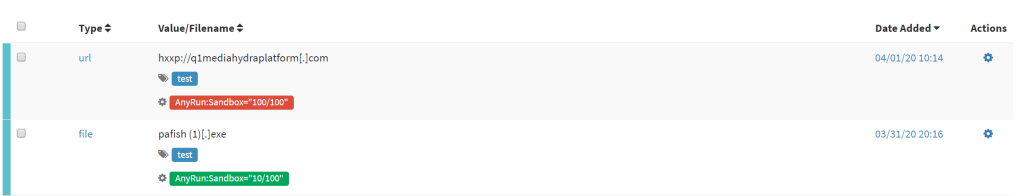
TheHive displays the analyzer results as follows:


ForcepointWebsensePing
Forcepoint URL Filtering provides defenses against productivity draining web content and threats to operations. It ensures organizational productivity by delivering defenses against productivity draining web activity while providing the necessary security in a world of advanced threats.
Using WebsensePing utility is possible to query Master Database URL Categories that contains the industry’s most accurate, current and comprehensive classification of URLs. ForcePoint uses proprietary classification software and human inspection techniques to categorize and maintain definitions of more than 95 URL categories in more than 50 languages.
An active Forcepoint subscription is required to use the analyzer.
TheHive displays the analyzer results as follows:


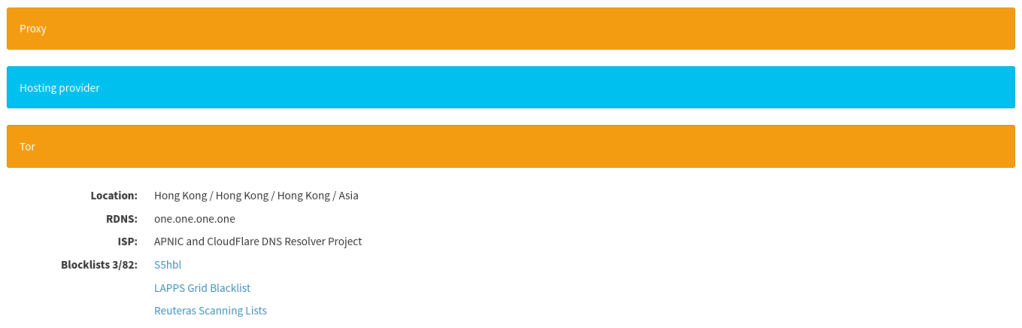
NERD
This analyzer allows to query the NERD (Network Entity Reputation) database, and get score and basic information. Project NERD aims to build an extensive reputation database of known sources of cyber threats. That is, a list of known malicious IP addresses or other network entities (e.g. ASNs or domain names) together with all security-relevant information about each of them.
A valid API key is required to run this analyzer.
TheHive displays the analyzer results as follows:


SekoiaIntelligenceCenter
This analyzer allows you to gather more context related to domain names, IP adresses, urls and file hashes using the SEKOIA.IO Intelligence Database.
An active SEKOIA.IO Intelligence Center subscription is required to use the analyzer.
TheHive displays the analyzer results as follows:

Spamassassin
This analyzer let you query a local SpamAssassin instance by sending a file, and get a SPAM score.
Apache SpamAssassin is the #1 Open Source anti-spam platform giving system administrators a filter to classify email and block spam (unsolicited bulk email). It uses a robust scoring framework and plug-ins to integrate a wide range of advanced heuristic and statistical analysis tests on email headers and body text including text analysis, Bayesian filtering, DNS blocklists, and collaborative filtering databases.
TheHive displays the analyzer results as follows:


Splunk
This analyzer allows you to execute a list of searches in Splunk by passing the element you are looking for as a parameter.
This analyzer comes in 10 flavors:
- Splunk_Search_Domain_FQDN: Dispatch a list of saved searches on a given
domain/fqdn - Splunk_Search_File_Filename: Dispatch a list of saved searches on a given
file/filename - Splunk_Search_Hash: Dispatch a list of saved searches on a given
hash - Splunk_Search_IP: Dispatch a list of saved searches on a given IP (IPv4 only)
- Splunk_Search_Mail_Email: Dispatch a list of saved searches on a given
mail/email - Splunk_Search_Mail_Subject: Dispatch a list of saved searches on a given
mail_subject - Splunk_Search_Other: Dispatch a list of saved searches on a given data (any type)
- Splunk_Search_Registry: Dispatch a list of saved searches on a given
registry - Splunk_Search_URL_URI_Path: Dispatch a list of saved searches on a given
url/uri_path - Splunk_Search_User_Agent: Dispatch a list of saved searches on a given
user_agent - Splunk_Search_User: Dispatch a list of saved searches on a given user id (variable name is ‘other’)
A valid Splunk subscription is required to run this analyzer.
TheHive displays the analyzer results as follows:


Responders
Velociraptor
Velociraptor let you interrogate your endpoint for specific data. Velociraptor is a tool for collecting host based state information using Velocidex Query Language (VQL) queries.
This responder can be used to run a flow for a Velociraptor artifact. This could include gathering data, or performing initial response.
It can be run on an observable type of ip, fqdn, or other, and will look for a matching client via the Velociraptor server. If a client match is found for the last seen IP, or the hostname, the responder will kick off the flow, the results will be returned, and the client ID will be added as a tag to the case and the observable.
Get It While Supply Lasts!
If you are still using the old-style way of installing analyzers and responders, run the following commands:
cd path/to/Cortex-Analyzers
git pull
for I in analyzers/*/requirements.txt; do sudo -H pip3 install -U -r $I || true; done
for I in responders/*/requirements.txt; do sudo -H pip3 install -U -r $I || true; done
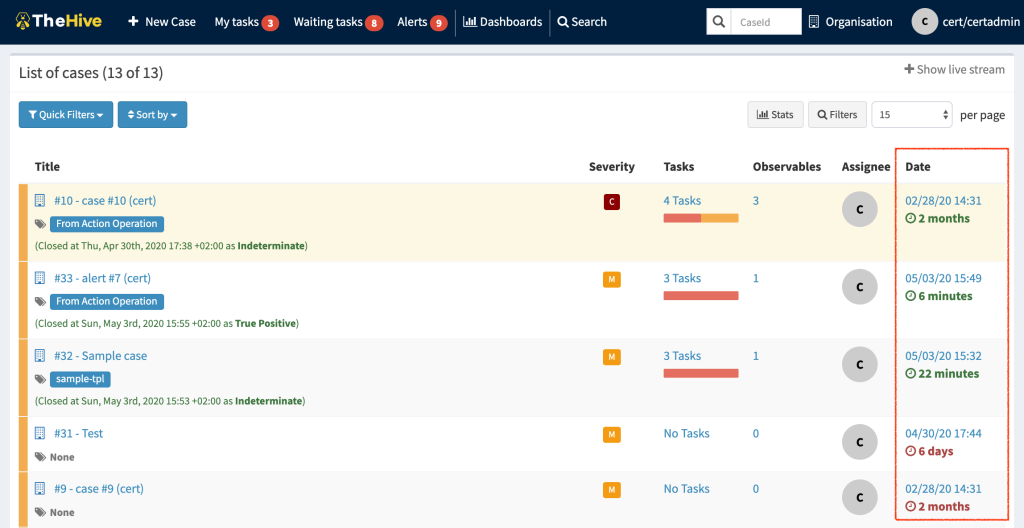
Once done, ensure to refresh your analyzers and responders in the Cortex WebUI. Connect as an orgadmin and go to the Organization menu. Click on the Analyzers tab and click on the Refresh analyzers button. Do the same for the Responders tab: click on the Refresh responders button. Refer to the online Cortex documentation for further details.
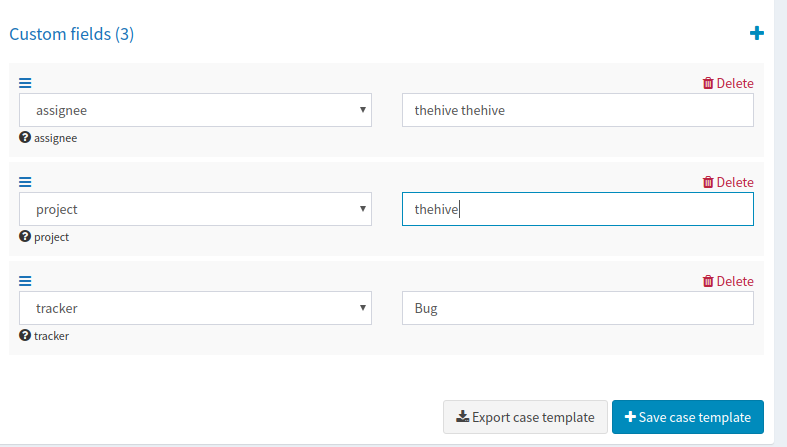
Update TheHive Report Templates
If you are using TheHive, you must import the new report templates in your instance as follows:
- download the updated package
- log in TheHive using an administrator account
- go to
Admin > Report templatesmenu (Admin > Analyzer templatesin TheHive 4.0) - click on
Import templatesbutton and select the downloaded package
Running Into Trouble?
Shall you encounter any difficulty, please join our user forum, contact us on Gitter, or send us an email at support@thehive-project.org. We will be more than happy to help!